Blog

Cybersecurity Basics Everyone Should Know
A comprehensive guide to essential cybersecurity practices covering password management, two-factor authentication, phishing prevention, safe browsing, and data backup for individuals and businesses.
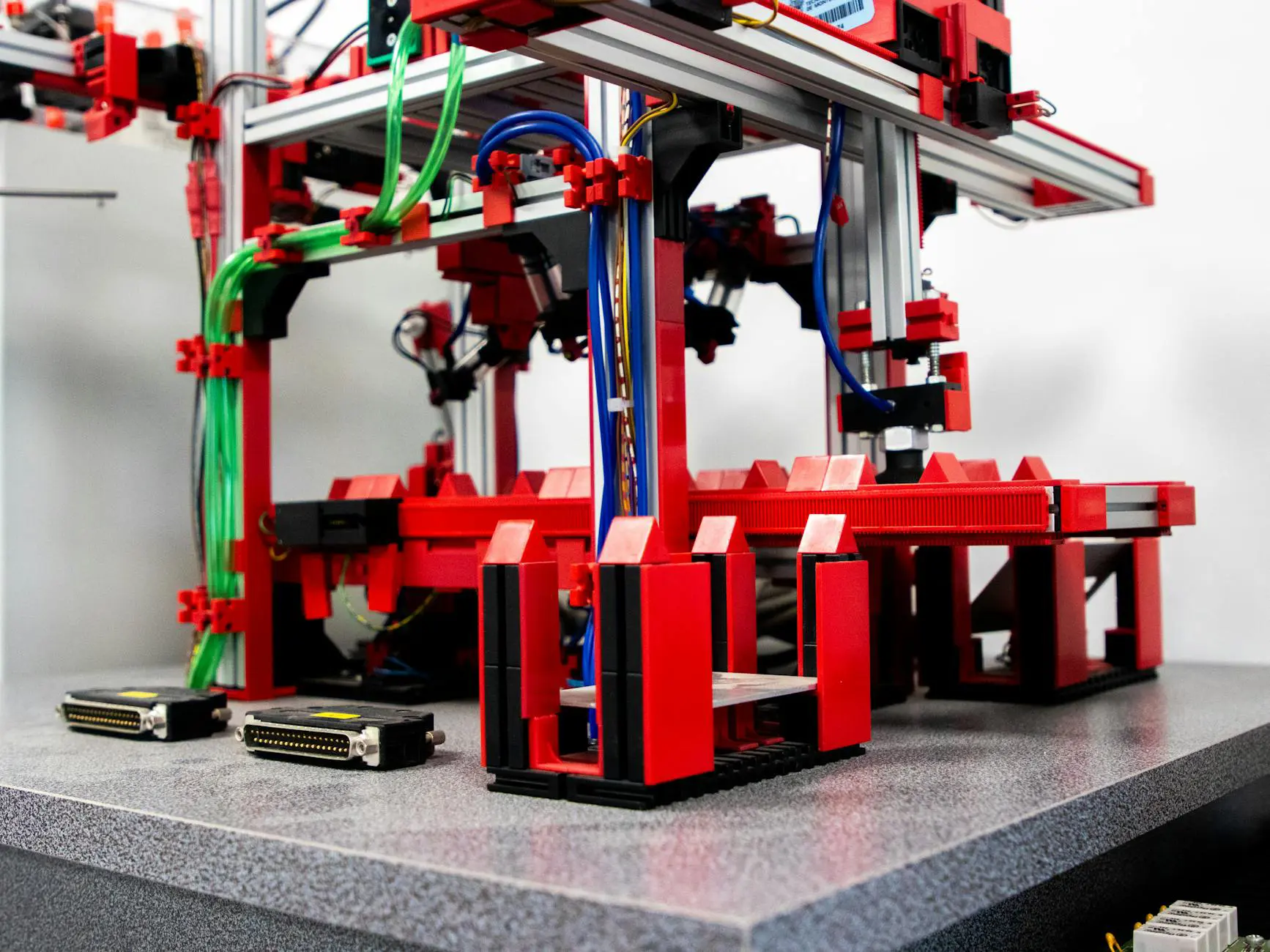
Software Testing Automation: Complete Guide
Automated testing is essential for fast, reliable software delivery. This complete guide covers the testing pyramid, frameworks, CI/CD integration, and strategies for writing maintainable automated tests.

Customer Retention Strategies for E-Commerce
Learn effective customer retention strategies for e-commerce including loyalty programs, personalized post-purchase experiences, exceptional customer service, subscription models, and win-back campaigns.
GraphQL vs REST: Choosing the Right API
GraphQL and REST take fundamentally different approaches to API design. Learn the strengths of each paradigm, when to use which, and how to choose the right architecture for your project.
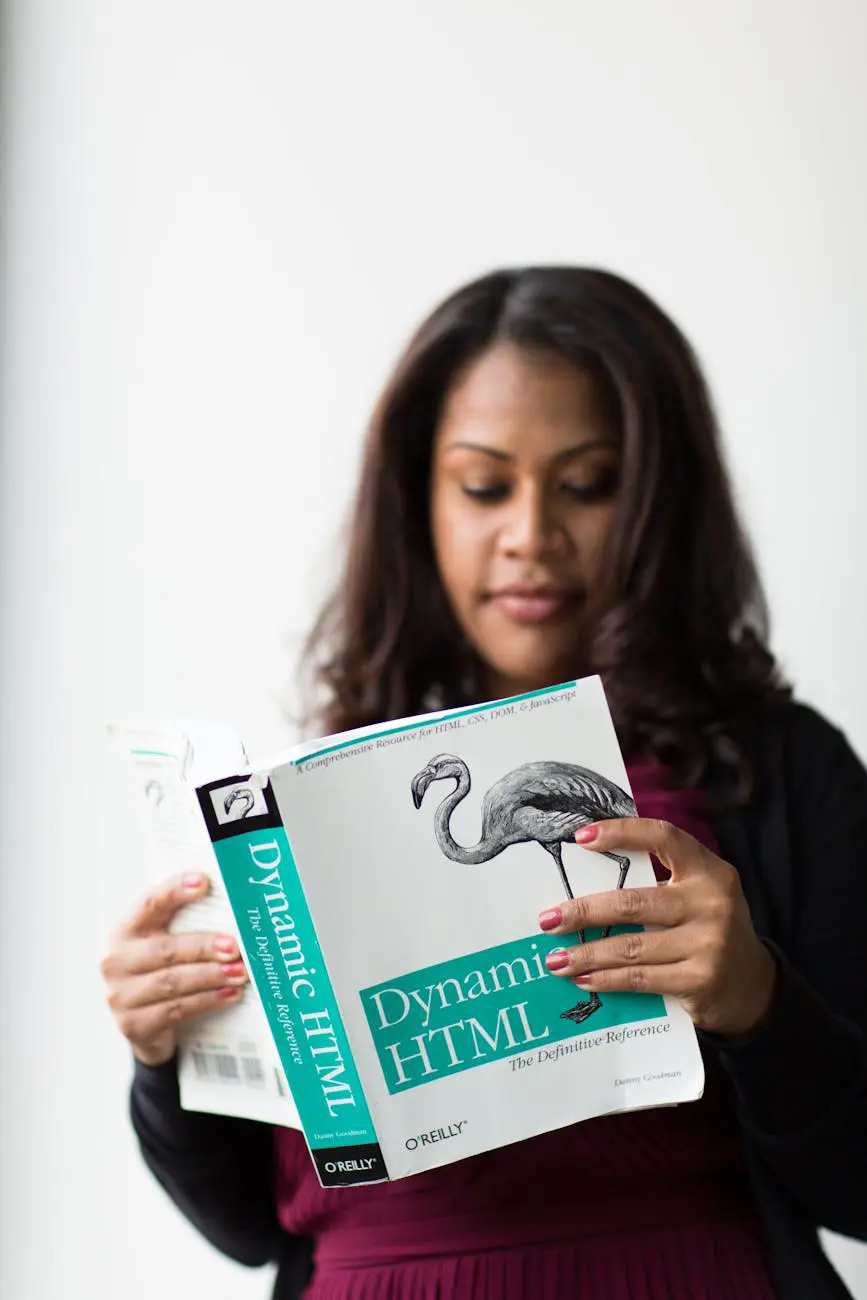
Web Accessibility (WCAG) Compliance Guide
A comprehensive guide to web accessibility and WCAG compliance. Learn the POUR principles, essential accessibility requirements, testing methods, legal obligations, and practical steps to make your website inclusive for all users.
NoSQL Databases Explained: When to Use Them
NoSQL databases offer flexible schemas, horizontal scaling, and specialized data models for use cases where relational databases fall short. This guide covers the four main types, compares them with SQL databases, and helps you decide when each is the right choice.

Flutter vs React Native: Which Is Better?
Flutter and React Native are the leading cross-platform mobile frameworks. This detailed comparison covers performance, UI rendering, ecosystem, learning curve, and real-world adoption to help you choose the right one for your project.

How to Increase Online Sales: Proven Strategies
Learn proven strategies to increase online sales through conversion optimization, checkout streamlining, cart recovery, upselling, email marketing, and site speed improvements.

API Security Best Practices for 2026
APIs are prime targets for cyberattacks. Learn essential security practices including OAuth 2.0 authentication, input validation, rate limiting, and monitoring to protect your APIs in 2026.